What Do I Get When I Turn on Microsoft Defender for Cloud?

Determine the cybersecurity return on investment in Microsoft Defender for Cloud.
Microsoft is very keen on selling their users security services like Microsoft Defender for Cloud, but it takes considerable effort and time to understand what each of them does. A Microsoft security admin assigned to Microsoft Defender for Cloud must also explain what Microsoft Defender for Cloud does for each of these resources to justify the additional expenditure.

In this blog, we will give a summary of what each of the Microsoft Defender for Cloud options does and how a person responsible for Microsoft security can calculate the security return on investment for turning each of these Microsoft Defender for Cloud options on.
Servers
This option turns on Microsoft Defender for Cloud for Windows and Linux VMs being hosted in the Microsoft Virtual Machines menu. This is the most robust Microsoft Defender for Cloud offering because of the high number of detections that become available. Microsoft put a sizable amount of effort into this offering because it is their cloud EDR solution for VMs.
The security return on investment can be calculated by using your organization’s Annualized Loss Expectancy (ALE) calculation and comparing that cost to the annual cost of $180 per VM. The VMs that have an ALE above $180 have a strong case for having Microsoft Defender for Cloud enabled.

Software Development Platforms
In these platforms Microsoft Defender for Cloud looks for signs of applications behaving in ways that may be a sign of compromise like commands found in the wrong area of an application, suspicious behavior, and unexpected processes.
The security return on investment can be calculated by using your organization’s Annualized Loss Expectancy (ALE) calculation and comparing that cost to the annual cost of $180 per app service, $24 per Kubernetes VM core, or $3.50 per container image.
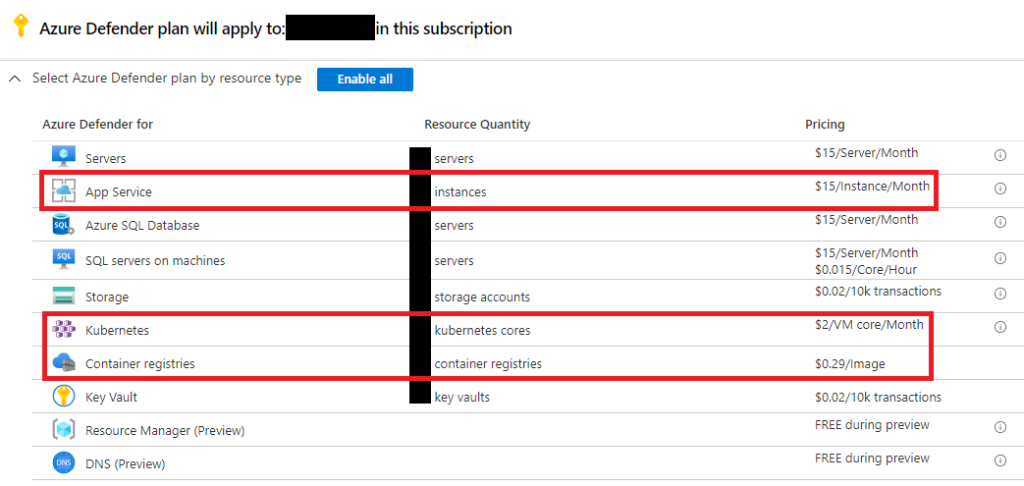
Storage Spaces
For each of these options Microsoft Defender for Cloud looks for signs of malicious activity in storage spaces like unexpected files found in storage, unusual volume of data movement, and unusual change in permissions.
The security return on investment can be calculated for SQL servers by using your organization’s Annualized Loss Expectancy (ALE) calculation and comparing that cost to the annual cost of $180 per SQL server. The Storage calculation is more complicated because it is based on transfer volume, the topic may need to be discussed with data custodians.
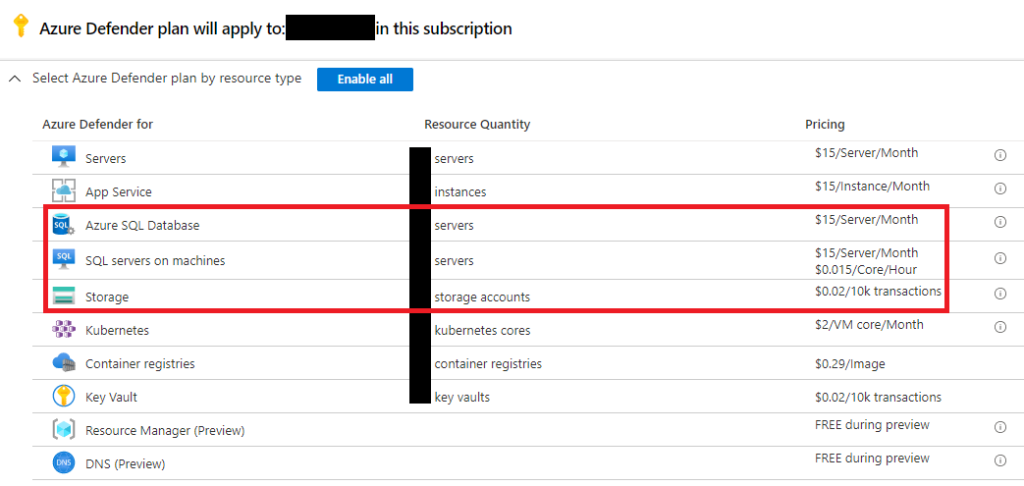
Key Vault
For this option Microsoft Defender for Cloud looks for signs of malicious activity like high volume of key vault operations, unusual key vault access patterns, and key vault activity from a known TOR node.
This option has the same issues as Storage where it uses transaction volume to determine the cost. The topic may need to be discussed with a data custodian and other security admins because secrets are a sensitive security issue.

Other
Microsoft Security Center is releasing new features in Microsoft Defender for Cloud regularly and while they are in preview Microsoft users get the opportunity to try them for free.
Despite the label saying “free” the alerts generated by the preview feature may take up the time of security analysts unnecessarily if they are not working as intended. It is up to security admins to determine if the value from preview features is worth the unintended costs.

We will continue to share best practices and lessons learned in future posts onMicrosoft Defender for Cloud in customer environments. When customers enable features like Microsoft Defender for Cloud, our job as a VSOC becomes easier, but that should not come at the unnecessary expense of our customers.
In closing, consider these three questions when determining if usingMicrosoft Defender for Cloud in your organization is worth the cost:
- Is there an accurate Annual Loss Expectancy (ALE) calculation that we can compare to Microsoft Defender for Cloud costs?
- How best to engage with business and IT stakeholders to help quantify the cybersecurity risk of cloud resources?
- How can we effectively communicate and justify the budget needed to enable Microsoft Defender for Cloud for our cloud resources?
