Why Aren’t My Microsoft Sentinel Playbooks Working?

Solutions to some common Playbook pitfalls.
Some of the error messages that appear in Playbooks are either very cryptic or simply unexplained because many Microsoft Sentinel Logic App components are in preview. Security analysts that are deploying Microsoft Sentinel Playbooks for the first time may see esoteric error messages like the example below and get discouraged.
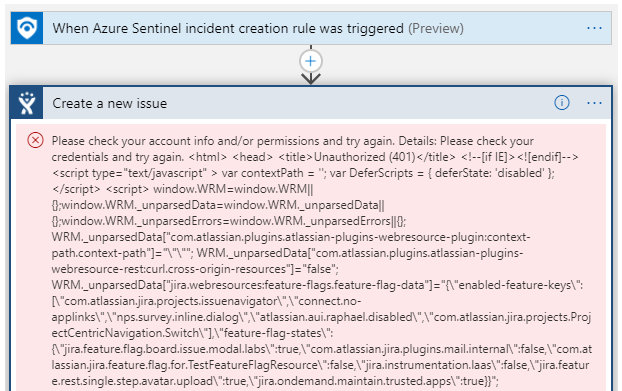
It takes persistence to push through nearly incomprehensible error messages from software that is functionally in beta. Therefore, you will need to be able to gather clues from the error messages and draw on any community resources that you can find.
In this blog, we share our experiences with troubleshooting Microsoft Sentinel Playbooks so that others will not have to spend precious time on these issues like we had to. This is not an exhaustive list of Microsoft Sentinel Playbook errors, but it covers the ones we see the most often along with the thought process needed to solve the issues that are preventing the Playbook from running.
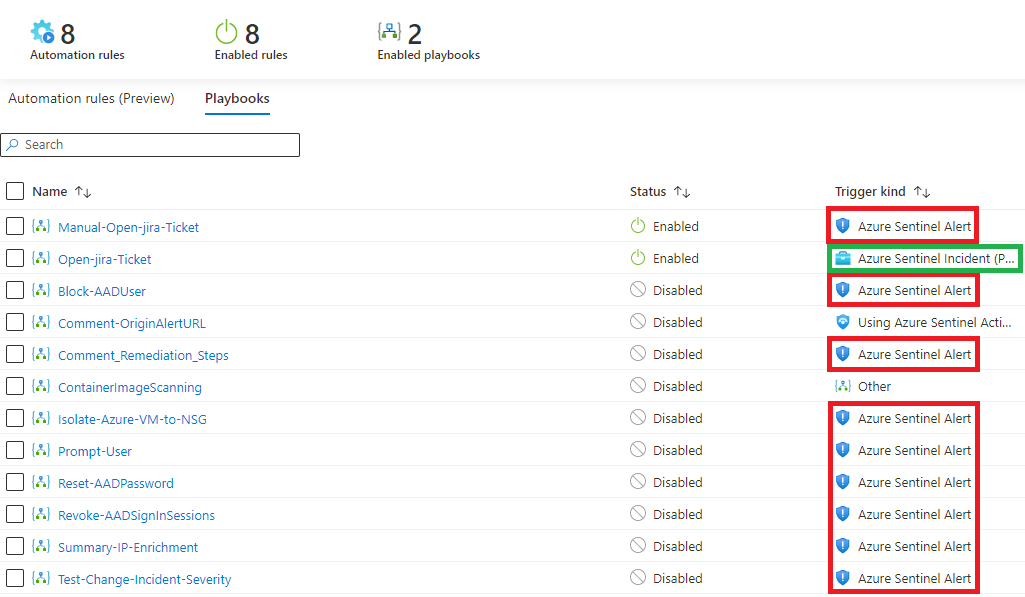
Playbooks not Appearing in Intended Menus
When a Playbook is first added it is common for analysts to want to use it right away in a test environment. Analysts would open one of the Sentinel menus that can use Playbooks only to discover that their new Playbook is not in that menu. The reason that Playbooks only appear in certain menus is because some Microsoft Sentinel menus only accept Playbooks with specific trigger types. The following list outlines the system used to determine where Playbooks appear.
Microsoft Sentinel Alerts: This Playbook trigger type is designed to be used manually when an analyst identifies an alert that they would like to take an action on. These Playbooks can be found in the Alerts menu of any Sentinel incident. In the screenshot below, these are outlined in red.
Microsoft Sentinel Incidents: This Playbook trigger type is designed to be used automatically when an analytic rule identifies an incident. These playbooks can be found in the Automated Response menu of analytic rules. In the example image they are highlighted in green.
Other: All the other Playbook triggers use something other than Sentinel for their trigger. They will not appear anywhere in Sentinel aside from the Playbooks menu.
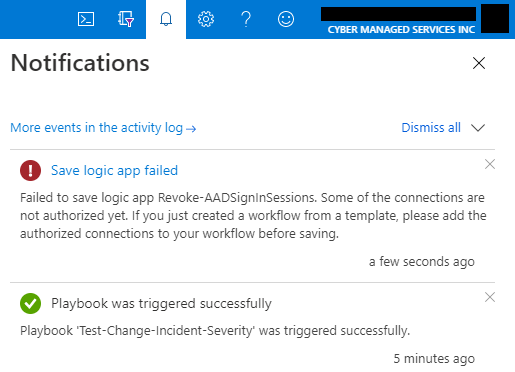
“Save Logic App Failed”
When attempting to save a Playbook, a Microsoft Sentinel user may be prevented from doing so by an error message. This error normally appears when the connectors for one of the Logic Apps does not have enough permissions to finish the action in a logic app piece. A Microsoft Sentinel user can fix this issue by creating a service principal or service connection with the privileges needed to fulfill the actions outlined in the Playbook. Once the service principal or service connection is ready, the user can change the connection to the logic app pieces and attempt to save the Playbook again.
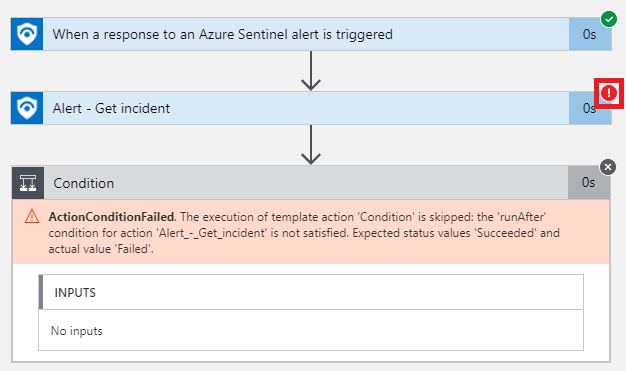
“Action Condition Failed”
When a control action piece like “condition” or “for each” fails with this error message, the issue is not actually with the action piece. The error message only appeared on that action piece because a piece before it had an error message. When an Microsoft Sentinel user runs into this issue, look for the error indicator in the top-right corner of all the pieces before the control action piece. If the action piece with a red exclamation point in the top-right corner is fixed, the “action condition failed” error should also be fixed.
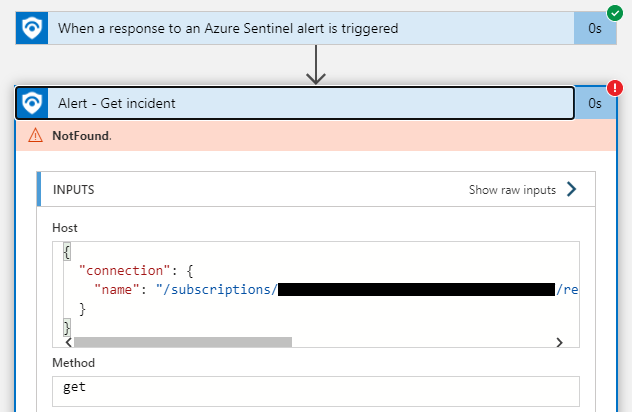
“Not Found”
This error appears when a value that an action piece is expecting to receive does not appear and it crashes as a result. There are 2 common explanations for what is causing this issue.
Run Trigger Button: The button available at the top left of the Playbook menu that is used for testing may cause this error on a working Playbook. This happens because the Playbook needs a value that is coming out blank because no data comes out of the Run Trigger button. Run the Playbook in a test environment to see if this is the issue.
Invalid Input: The Playbook may have the wrong value or variable being inserted into one of the sections of an action piece. Double-check the values and variables input into the action piece to ensure that they are supposed to be used where they are currently inserted.
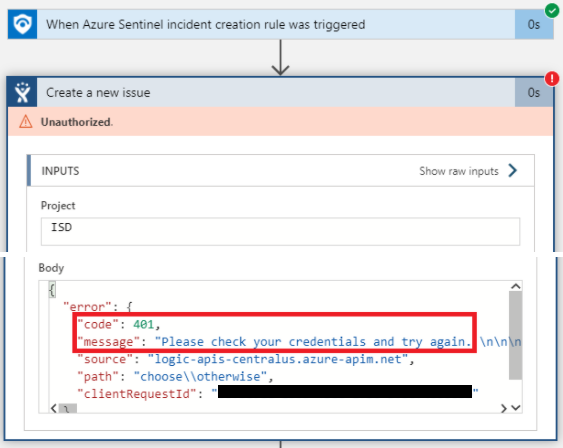
“Unauthorized”
This is an error that appears when a service connection is created successfully but the connection is either not allowed to take an action on a service or is misconfigured. Check both the service connection configurations and the permissions associated with the identity used for the service connection. The “Body” section of the error is particularly useful because it displays a raw output of the error message.
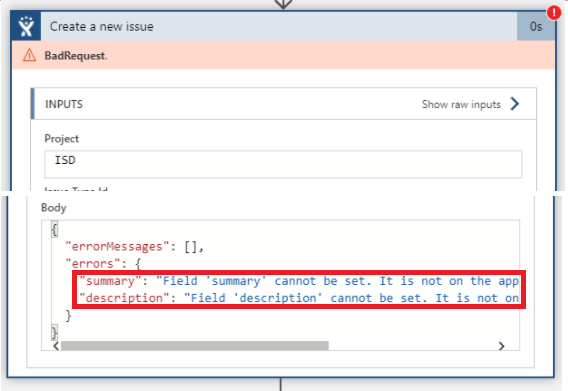
“Bad Request”
This is an error that appears if there is an issue with an API call to another service. This is a difficult error because there are more types of API calls than there are people that understand APIs.To address an issue with so many potential causes, the Microsoft Sentinel user will have to go through the raw error output in the “Body” section of the error. Once the error is identified, they can use context clues from that error and google searches related to the error to determine how they can fix their specific API call issue.
We will continue to share best practices and lessons learned in future posts on using Microsoft Sentinel Playbooks in customer environments. Errors in Playbooks may seem intimidating, but they can be surmounted with ingenuity and support from the Microsoft Sentinel community.
In closing, consider these three questions when troubleshooting Playbooks in your organization:
- How can I use context clues to navigate through issues that Google searches cannot solve?
- Do we have sufficient cybersecurity incident data to thoroughly test our Playbooks before deploying them to production?
- How can we address the skills gap on our team that is preventing us from solving more complex issues like invalid inputs or failed API calls?
